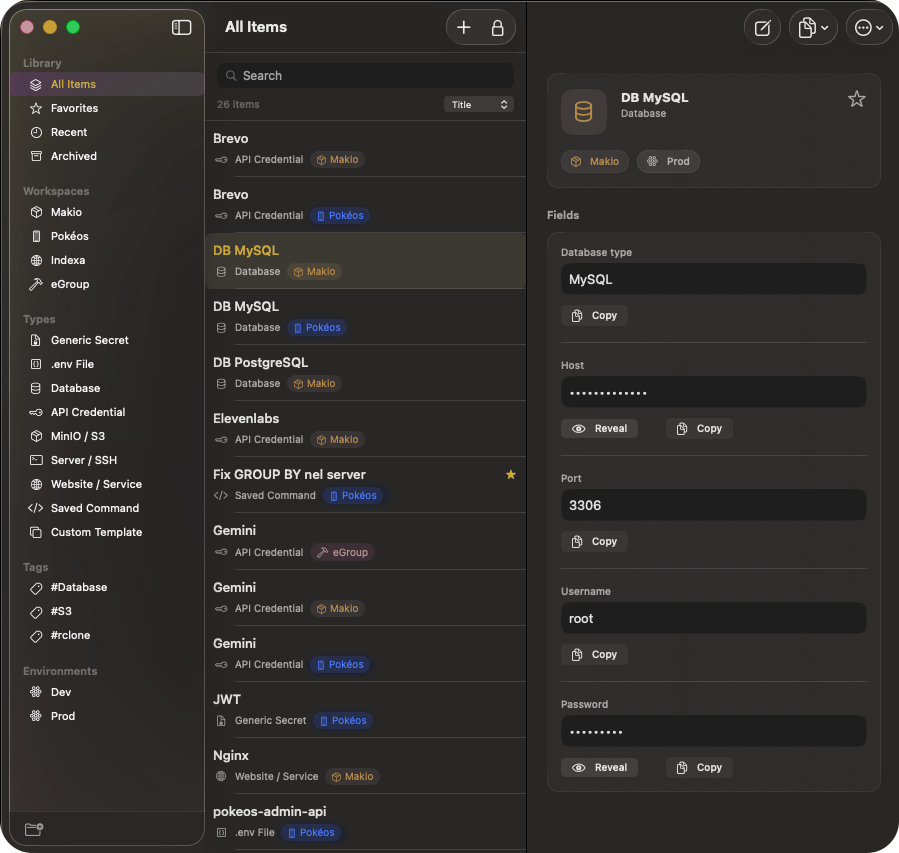
Local-first vault
API keys, database credentials, and .env groups stay on your Mac. No cloud sync, no telemetry, no vendor lock-in — sensitive values in Keychain, not plain text in the database, plus encryption at rest.
- Keychain-ready
- AES-256-GCM at rest
- You own the data
Nothing phones home while you work — exports are explicit, under your control.